IT Blog
Technologies You Need If You’re Going to Use Remote Workers
Does your business use remote workers? If you currently don’t, you should know that there are several benefits of allowing your staff to work outside of the confines of your office, but you have to be careful. These days, with the threat landscape as it is, it is...
Phishing is a Major Threat
Fishing - a jerk on one end of a line waiting for a jerk on the other end.Phishing - very similar to fishing, but much more consequential. While the word phishing is humorous and relatable due to it being derived from the word “fishing”, the consequences of falling...
Get the Utility You Need From the Cloud
If you’ve ever moved files from a flash drive, you are likely well aware at how troublesome limited storage space can be. Business data storage is no different, however the flash drives transition into servers, and the $10 tech store purchase transitions to thousands...
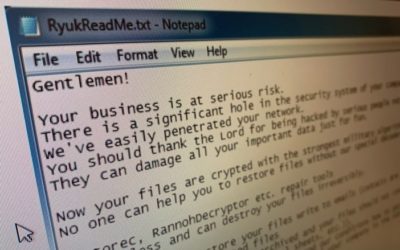
3 Ontario Hospitals hit by ransomware
Hackers have crippled the computer systems of three Ontario hospitals in recent weeks, prompting concern about the type of malicious software used and whether more facilities may be at risk. The malware, known as "Ryuk," attacks computer networks but remains invisible...
Best Practices for Your File Sharing and Collaboration Needs
Today, a business accumulates a lot - a lot - of files as time passes, and for the most part, they all need to be stored somewhere. In addition to that, there’s a good chance that multiple people will need to remain involved with these files. These challenges can be...
Tip of the Week: Methods to Securing Your Smartphone
The smartphone has quickly become a staple in modern society, as users rely on them to accomplish more and more. You could probably say the same of your own use of it. This means that there are not only huge amounts of smartphones and smartphone users, there is a huge...
Why Proactivity is Always a Better Strategy than Reactivity
When it comes to operating a business, there are really only two ways that one can do so… either one acts proactively with their business matters, or they tend to be reactive in their approach. Naturally, one method has shown to be far more effective than the other....
No More Pencils, No More Books… Examining Technology in Education
While we typically write about matters that concern your business and its use of technology in this blog, we decided to do something a little different today. Someday in the not-so-distant future, today’s students will make up the workforce, and their educations are...
Woodstock Ontario city targeted by ransomware
First published September 23, 2019, The City of Woodstock and the Woodstock Police Service are both suffering cyber attacks. Woodstock’s top administrator, David Creery, confirmed the city had a network breach early Saturday, September 21 around 4 a.m. when a virus...
Tip of the Week: How to Set Up Android Work Profiles
How many of your employees have a personal device that they want to leverage in the workplace? There are a few ways that this can be enabled that doesn’t put your data at risk, and that don’t keep the employee from being able to use their device the way they want to...